Cybersecurity researchers are calling attention to a spike in automated attacks targeting PHP servers, IoT devices, and cloud gateways by various botnets such as Mirai, Gafgyt, and Mozi.
“These automated campaigns exploit known CVE vulnerabilities and cloud misconfigurations to gain control over exposed systems and expand botnet networks,” the Qualys Threat Research Unit (TRU) said in a report shared with The Hacker News.
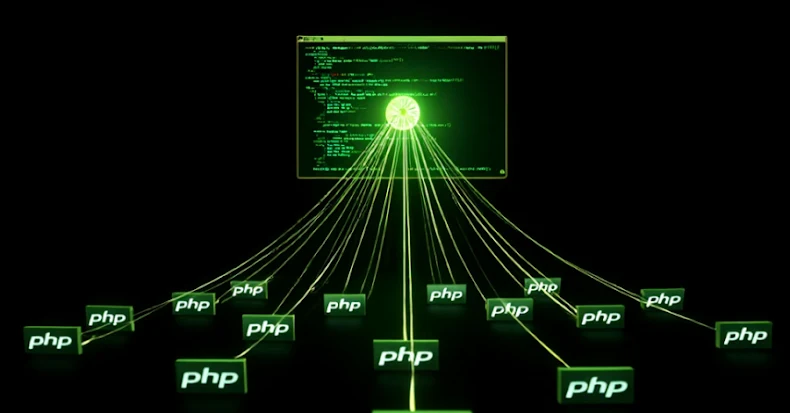
The cybersecurity company said PHP servers have emerged as the most prominent targets of these attacks owing to the widespread use of content management systems like WordPress and Craft CMS. This, in turn, creates a large attack surface as many PHP deployments can suffer from misconfigurations, outdated plugins and themes, and insecure file storage.
Some of the prominent weaknesses in PHP frameworks that have been exploited by threat actors are listed below –
- CVE-2017-9841 – A Remote code execution vulnerability in PHPUnit
- CVE-2021-3129 – A Remote code execution vulnerability in Laravel
- CVE-2022-47945 – A Remote code execution vulnerability in ThinkPHP Framework
Qualys said it has also observed exploitation efforts that involve the use of “/?XDEBUG_SESSION_START=phpstorm” query string in HTTP GET requests to initiate an Xdebug debugging session with an integrated development environment (IDE) like PhpStorm.
“If Xdebug is unintentionally left active in production environments, attackers may use these sessions to gain insight into application behavior or extract sensitive data,” the company said.
Alternatively, threat actors are continuing to look for credentials, API keys, and access tokens in internet-exposed servers to take control of susceptible systems, as well as leverage known security flaws in IoT devices to co-opt them into a botnet. These include –
- CVE-2022-22947 – A Remote code execution vulnerability in Spring Cloud Gateway
- CVE-2024-3721 – A Command injection vulnerability in TBK DVR-4104 and DVR-4216
- A Misconfiguration in MVPower TV-7104HE DVR that allows unauthenticated users to execute arbitrary system commands via an HTTP GET request
The scanning activity, Qualys added, often originates from cloud infrastructures like Amazon Web Services (AWS), Google Cloud, Microsoft Azure, Digital Ocean, and Akamai Cloud, illustrating how threat actors are abusing legitimate services to their advantage while obscuring their true origins.
“Today’s threat actors don’t need to be highly sophisticated to be effective,” it noted. “With widely available exploit kits, botnet frameworks, and scanning tools, even entry-level attackers can cause significant damage.”
To safeguard against the threat, it’s advised that users keep their devices up-to-date, remove development and debug tools in production environments, secure secrets using AWS Secrets Manager or HashiCorp Vault, and restrict public access to cloud infrastructure.
“While botnets have previously been associated with large-scale DDoS attacks and occasional crypto mining scams, in the age of identity security threats, we see them taking on a new role in the threat ecosystem,” James Maude, field CTO at BeyondTrust, said.
“Having access to a vast network of routers and their IP addresses can allow threat actors to perform credential stuffing and password spray attacks a huge scale. Botnets can also evade geolocation controls by stealing a user’s credentials or hijacking a browser session and then using a botnet node close to the victim’s actual location and maybe even using the same ISP as the victim to evade unusual login detections or access policies.”
The disclosure comes as NETSCOUT classified the DDoS-for-hire botnet known as AISURU as a new class of malware dubbed TurboMirai that can launch DDoS attacks that exceed 20 terabits per second (Tbps). The botnet primarily comprises consumer-grade broadband access routers, online CCTV and DVR systems, and other customer premise equipment (CPE).
“These botnets incorporate additional dedicated DDoS attack capabilities and multi-use functions, enabling both DDoS attacks and other illicit activities such as credential stuffing, artificial intelligence (AI)-driven web scraping, spamming, and phishing,” the company said.
“AISURU includes an onboard residential proxy service used to reflect HTTPS application-layer DDoS attacks generated by external attack harnesses.”
Turning compromised devices into a residential proxy allows paying customers to route their traffic through one of the nodes in the botnet, offering anonymity and the ability to blend in with regular network activity. According to independent security journalist Brian Krebs, all of the major proxy services have grown exponentially over the past six months, citing data from spur.us.