A malicious network of YouTube accounts has been observed publishing and promoting videos that lead to malware downloads, essentially abusing the popularity and trust associated with the video hosting platform for propagating malicious payloads.
Active since 2021, the network has published more than 3,000 malicious videos to date, with the volume of such videos tripling since the start of the year. It has been codenamed the YouTube Ghost Network by Check Point. Google has since stepped in to remove a majority of these videos.
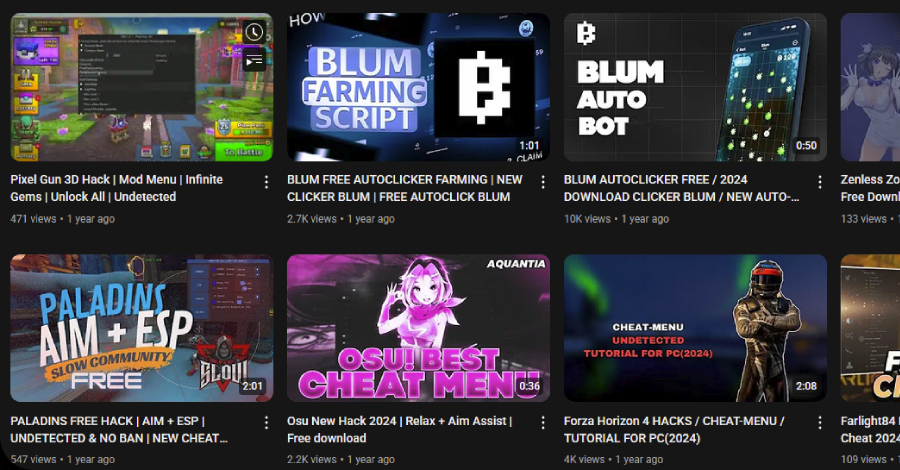
The campaign leverages hacked accounts and replaces their content with “malicious” videos that are centred around pirated software and Roblox game cheats to infect unsuspecting users searching for them with stealer malware. Some of these videos have racked up hundreds of thousands of views, ranging from 147,000 to 293,000.
“This operation took advantage of trust signals, including views, likes, and comments, to make malicious content seem safe,” Eli Smadja, security research group manager at Check Point, said. “What looks like a helpful tutorial can actually be a polished cyber trap. The scale, modularity, and sophistication of this network make it a blueprint for how threat actors now weaponize engagement tools to spread malware.”
The use of YouTube for malware distribution is not a new phenomenon. For years, threat actors have been observed hijacking legitimate channels or using newly created accounts to publish tutorial-style videos with descriptions pointing to malicious links that, when clicked, lead to malware.
These attacks are part of a broader trend where attackers repurpose legitimate platforms for nefarious purposes, turning them into an effective avenue for malware distribution. While some of the campaigns have abused legitimate ad networks, such as those associated with search engines like Google or Bing, others have capitalized on GitHub as a delivery vehicle, as in the case of the Stargazers Ghost Network.
One of the main reasons why Ghost Networks has taken off in a big way is that they can not only be used to amplify the perceived legitimacy of the links shared, but also maintain operational continuity even when the accounts are banned or taken down by the platform owners, thanks to their role-based structure.
“These accounts take advantage of various platform features, such as videos, descriptions, posts (a lesser-known YouTube feature similar to Facebook post), and comments to promote malicious content and distribute malware, while creating a false sense of trust,” security researcher Antonis Terefos said.
“The majority of the network consists of compromised YouTube accounts, which, once added, are assigned specific operational roles. This role-based structure enables stealthier distribution, as banned accounts can be rapidly replaced without disrupting the overall operation.”
There are three specific types of accounts –
- Video-accounts, which upload phishing videos and provide descriptions containing links to download the advertised software (alternatively, the links are shared as a pinned comment or provided directly in the video as part of the installation process)
- Post-accounts, which are responsible for publishing community messages and posts containing links to external sites
- Interact-accounts, which like and post encouraging comments to give the videos a veneer of trust and credibility
The links direct users to a wide range of services like MediaFire, Dropbox, or Google Drive, or phishing pages hosted on Google Sites, Blogger, and Telegraph that, in turn, incorporate links to download the supposed software. In many of these cases, the links are concealed using URL shorteners to mask the true destination.
Some of the malware families distributed via the YouTube Ghost Network include Lumma Stealer, Rhadamanthys Stealer, StealC Stealer, RedLine Stealer, Phemedrone Stealer, and other Node.js-based loaders and downloaders –
- A channel named @Sound_Writer (9,690 subscribers), which has been compromised for over a year to upload cryptocurrency software videos to deploy Rhadamanthys
- A channel named @Afonesio1 (129,000 subscribers), which was compromised on December 3, 2024, and January 5, 2025, to upload a video advertising a cracked version of Adobe Photoshop to distribute an MSI installer that deploys Hijack Loader, which then delivers Rhadamanthys
“The ongoing evolution of malware distribution methods demonstrates the remarkable adaptability and resourcefulness of threat actors in bypassing conventional security defenses,” Check Point said. “Adversaries are increasingly shifting toward more sophisticated, platform-based strategies, most notably, the deployment of Ghost Networks.”
“These networks leverage the trust inherent in legitimate accounts and the engagement mechanisms of popular platforms to orchestrate large-scale, persistent, and highly effective malware campaigns.”